Conrad Sallian's community posts
Untrusted Certificate ?
Conrad Sallian,
Support (Posts: 3190)
Apr 06, 2020 6:05:54 am EDT
Hi John,
On that Comodo KB page there was a link to another article:
Why does the secure part of the website say the name on the security certificate is invalid or does not match the name of the site?
Please, check it out. This issue is an issue on a specific computer/web browser, not a server issue. Otherwise, we would already be receiving complaints.
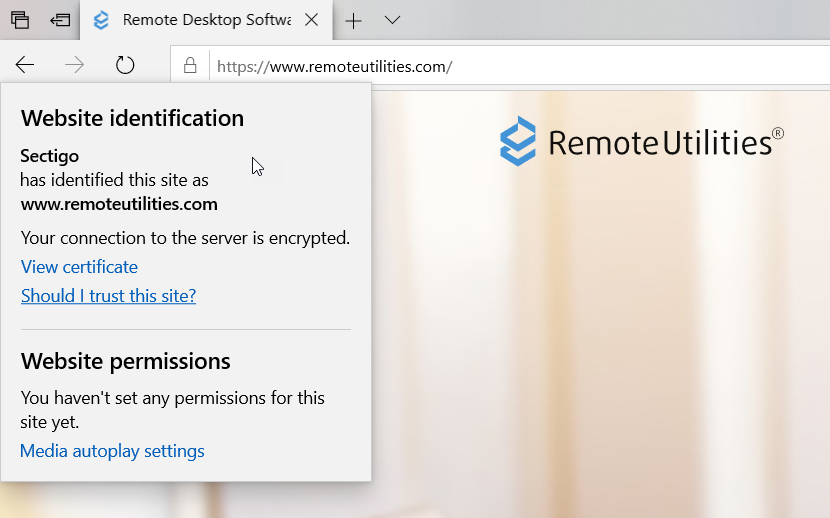
Here is how the site shows in Edge:
On that Comodo KB page there was a link to another article:
Why does the secure part of the website say the name on the security certificate is invalid or does not match the name of the site?
Please, check it out. This issue is an issue on a specific computer/web browser, not a server issue. Otherwise, we would already be receiving complaints.
Here is how the site shows in Edge:
Beta testing: Remote Utilities for macOS/Linux
Conrad Sallian,
Support (Posts: 3190)
Apr 06, 2020 5:59:46 am EDT
Hi Nick,
We are working hard on delivering on this promise :) Thank you for your support.
We are working hard on delivering on this promise :) Thank you for your support.
Error on opening the application
Conrad Sallian,
Support (Posts: 3190)
Apr 06, 2020 5:57:51 am EDT
Hi Neil,
Thank you for your message.
Your Viewer configuration file may have been corrupted. Please, close the Viewer, access the folder %APPDATA%\Roaming\Remote Utilities Files\ and delete the file config_4.xml. Then start the Viewer. The config file will get regenerated anew.
As for speed/performance, please refer to this KB article.
Hope that helps.
Thank you for your message.
Your Viewer configuration file may have been corrupted. Please, close the Viewer, access the folder %APPDATA%\Roaming\Remote Utilities Files\ and delete the file config_4.xml. Then start the Viewer. The config file will get regenerated anew.
As for speed/performance, please refer to this KB article.
Hope that helps.
Untrusted Certificate ?
Conrad Sallian,
Support (Posts: 3190)
Apr 04, 2020 11:57:25 am EDT
Hi John,
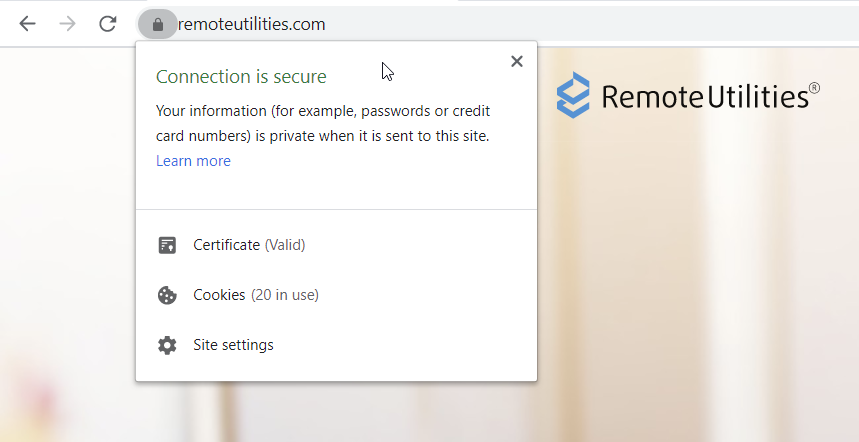
Here are screenshots from Chrome Version 80.0.3987.149 (Official Build) (64-bit) that I've just taken:
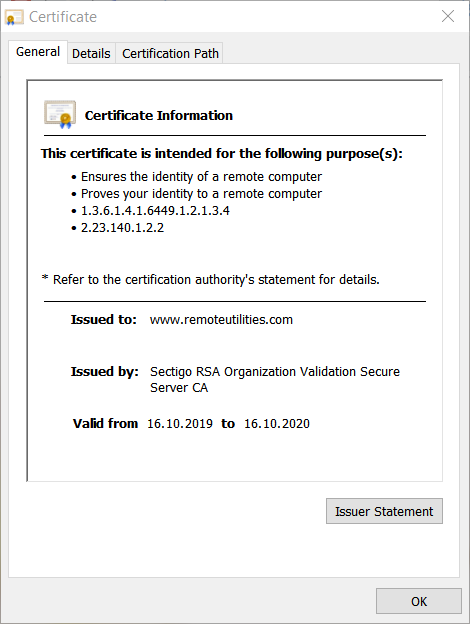
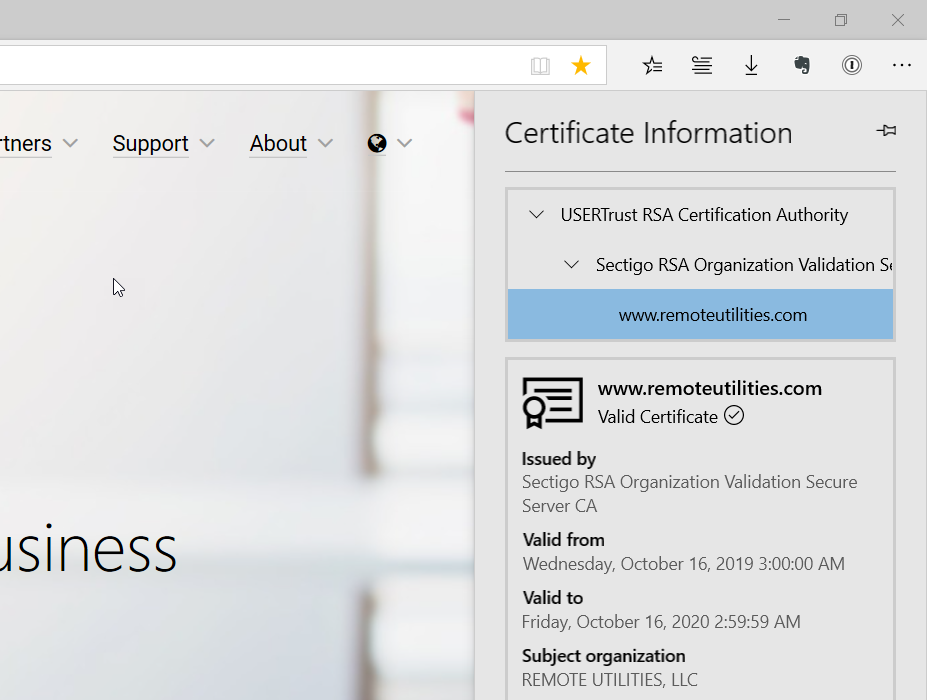
Perhaps, there is an issue with root or intermediate certificate. Your certification path should look as follows:
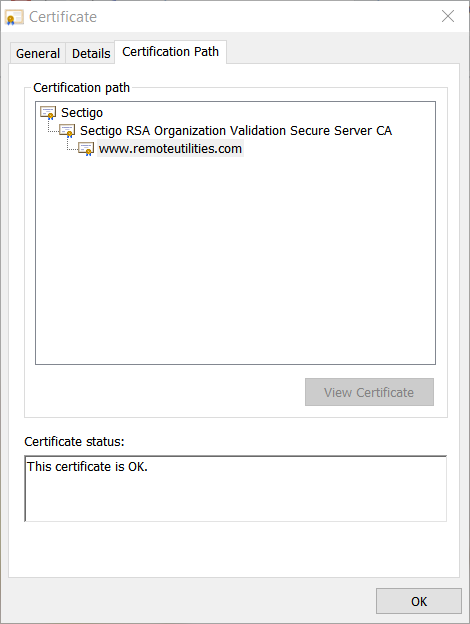
Here is a Comodo knowledge base article on the subject.
P.S. Sectigo is Comodo's new brand name.
Here are screenshots from Chrome Version 80.0.3987.149 (Official Build) (64-bit) that I've just taken:
Perhaps, there is an issue with root or intermediate certificate. Your certification path should look as follows:
Here is a Comodo knowledge base article on the subject.
P.S. Sectigo is Comodo's new brand name.
Beta testing: Remote Utilities for macOS/Linux
Conrad Sallian,
Support (Posts: 3190)
Apr 03, 2020 11:58:45 am EDT
Hi Cosmos,
Address book encrypted aren't supported on Mac and Linux platforms yet. We'll be adding that feature a bit later. Sorry for any inconvenience.
Address book encrypted aren't supported on Mac and Linux platforms yet. We'll be adding that feature a bit later. Sorry for any inconvenience.
Access to one PC by multiple users.
Conrad Sallian,
Support (Posts: 3190)
Apr 03, 2020 6:17:13 am EDT
Hello Rob,
Thank you for your message.
Unfortunately, so far there isn't any scheduled access capabilities, but this feature is on our wish list. However, you can already see how many active Viewers are currently being connected to a certain Host if you enable the notification panel.
Hope that helps.
Thank you for your message.
Unfortunately, so far there isn't any scheduled access capabilities, but this feature is on our wish list. However, you can already see how many active Viewers are currently being connected to a certain Host if you enable the notification panel.
Hope that helps.
Google Authenticator app susceptible to malware attacks
Conrad Sallian,
Support (Posts: 3190)
Apr 01, 2020 12:53:36 pm EDT
Hello Scott,
Thank you for your message.
You can use Microsoft Authenticator. Personally, I found it more user-friendly and easy to use. Try that and you'll see.
https://www.microsoft.com/en-us/account/authenticator
Thank you for your message.
You can use Microsoft Authenticator. Personally, I found it more user-friendly and easy to use. Try that and you'll see.
https://www.microsoft.com/en-us/account/authenticator
Laggy due to increase in work-at-home -- coronavirus
Conrad Sallian,
Support (Posts: 3190)
Mar 29, 2020 1:13:08 pm EDT
Hi Robert,
Unfortunately, no. However, the program can detect whether there is direct connectivity between Viewer and Host and use direct route even if you use Internet-ID connection.
Unfortunately, no. However, the program can detect whether there is direct connectivity between Viewer and Host and use direct route even if you use Internet-ID connection.
Laggy due to increase in work-at-home -- coronavirus
Conrad Sallian,
Support (Posts: 3190)
Mar 29, 2020 5:42:31 am EDT
Hello Everyone,
Ever since this pandemic started we have expanded our server network significantly to compensate for the sudden increase in demand for our software. I'm sure many of our competitors had to do the same thing.
Besides, RU servers are spread out across North America and Europe and in most cases the connection is routed via the server closest to the customer.
Thanks.
Ever since this pandemic started we have expanded our server network significantly to compensate for the sudden increase in demand for our software. I'm sure many of our competitors had to do the same thing.
Besides, RU servers are spread out across North America and Europe and in most cases the connection is routed via the server closest to the customer.
Thanks.
PRO License [Full silent install]
Conrad Sallian,
Support (Posts: 3190)
Mar 29, 2020 5:30:58 am EDT
Hi Manuel,
Thank you for your message. This feature is explained here .
Hope that helps.
Thank you for your message. This feature is explained here .
This is possible, of course, but it has nothing to do with full silent install in a sense which is used in the license comparison page. Full silent install simply means that the remote user won't be seeing a warning message the first time the Host is run.Does this mean that the client can be installed on a windows machine without the installation window?
Yes, just utilize the SMTP mailsend feature in the MSI configuration step 3.Is there a way to receive the client ID remotely without being logged in on the machine I'm installing the client?
Hope that helps.