Understanding Common Protocols: The OSI Model
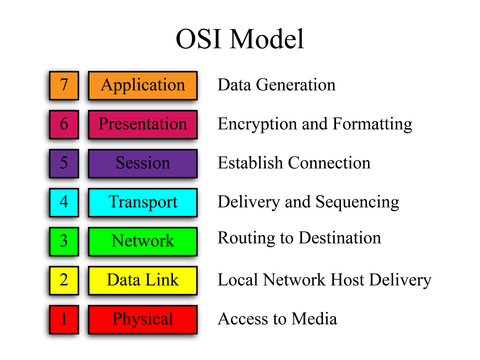
How much do you know about your network protocols? One of the most common network protocols you will encounter is the OSI model, which stands for Open System Interconnection. This model uses seven layers to connect multiple systems on the same network. Understanding the different layers of the OSI model is one step on the way to being able to implement this protocol in the most efficient way possible.
The Application Layer
This is actually the last layer of the OSI model, but is the most important to understand. The application layer identifies communication partners and the quality of service. It also handles user authentication and privacy issues. Every function used in this layer is tailored to a specific application and designed to provide the best end user experience possible. Some services provided by this layer include email, file transfers, and network security. Tiered application architectures and FTP processes are also handled by this layer.
The Presentation Layer
Different computers have different visual representations of data, and those differing visuals need to be reconciled somehow. The presentation layer translates information from a device to a format that can be read by the network and then to something that can be read by another receiving device. All encryption happens on this level, which means it has the double purpose of translating data and keeping it secure from machines that should not have access to the information being sent.
The Session Layer
Every application needs a protocol that connects it to other programs that are running at the same time. The session layer handles all of these program interactions. You can think of it as a sort of task manager for your network, handling all the communication and exchanges between different programs. It makes adjustments as each application begins and ends. This application also coordinates connections to the network, managing the changes in different protocols as each new set of software begins and altering things again when a user logs off.
The Transport Layer
When information gets sent from one program or computer to another, the transport layer makes sure that the data flow doesn’t get interrupted. If an error does occur and data is disrupted, this layer exists to properly report that error, recover the lost data, and re-establish the connection. Without this layer in place, there would be no protection from a dropped connection or crash during data transfer. That would mean a lot of permanently lost or corrupted data and a major efficiency crisis for your business network.
The Network Layer
The network layer is the routing site for most network activity. This layer routes data and transmits it from point to point along your network. It creates logical paths for information to follow. These paths are also known as virtual circuits. This layer also handles network addresses, error handling, and packet sequencing. It manages congestion control, making sure that activity on one part of the network does not interfere with the rest of the network’s performance. If you are having data or slowdown issues, this layer may be the one you want to look at first.
Data Link Layer
This layer represents the starting point for most data that gets routed on through the network. The data link layer takes all data packets and encodes or decodes them into a language that the network can understand and use. This layer has two sub-layers you should be aware of. The Media Access Control, or MAC, sub-layer controls how a network gains permission to transmit data. The Logical Link Control, or LLC, sub-layer manages frame synchronization, flow control, and error checking.
Physical Layer
No matter how your information is transmitted, it always goes through physical hardware. The physical layer manages the conversion from hardware to software, targeting the adaptation of information into data. This layer includes all the electronics and mechanical parts of a network, particularly routers and server controls. All information begins at the physical layer, and then passes through each of the layers listed above as it gets transmitted from place to place on your network.
The reason that knowing about the OSI model is very useful is because it gives you a sort of roadmap as to how your network works. That way, if you run into any problems with your network you have at least some idea of which layer the issue is likely occurring on. By being able to isolate the problem somewhat, you will be better equipped to fix any problems that might arise on your network.